RISK ENGINE FOR SKYPE-FOR-BUSINESS
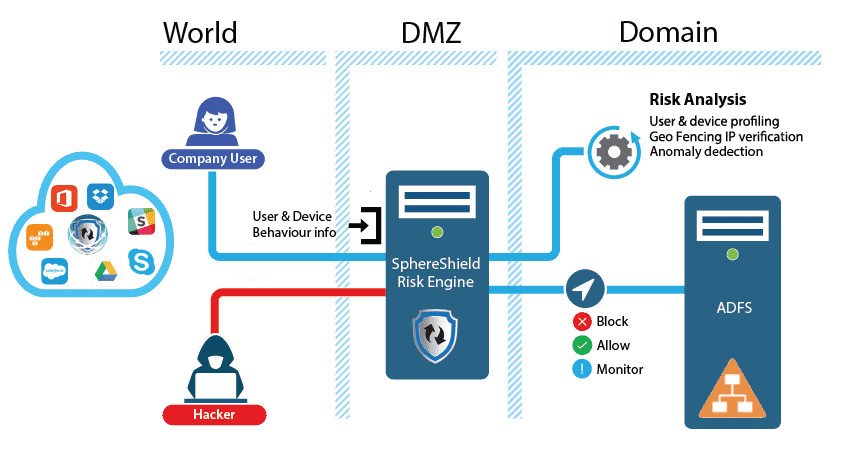
SphereShield’s Risk Engine module employs a set of tools designed to provide significant assurance as to the legitimacy of traffic entering the network. The Risk Engine preforms security assessments based on data such as geo-location and profiling of user behavior.
The Risk Engine plays a key role in governing access to a network, helping ensure accountability in business communication.
Performing risk assessment of online activities and rendering intelligent decisions based on that knowledge, are essential in securing a corporate network. The ability to determine which transactions to allow through, which ones to monitor, and which ones to deny, is crucial in protecting against fraudulent communication attempts.
Risk Engine takes action to monitor, alert as atypical or suspicious, and—where necessary—block network traffic when a high likelihood of exposure risk, fraudulent activity,or intrusive intent have been detected. Deploying the Risk Engine reduces exposure, protects privacy, detects impersonation, lowers occurrence of unwarranted access, and identifies trends in fraudulent activities as they occur.

· Machine learning – combining self-learning, feedback loops, scoring algorithms, and statistics
· Behavioral analysis – determining if attempted activities are typical for a particular user of the network, if they’re atypical, or even impossible
· Duration of use
· Type of activities, such as file transfer and desktop sharing
· Client types, for instance mobile phones and PCs
· Extending Risk Engine’s network profiling and anomaly discovery capabilities by detecting large data capacities being transferred across a network.