EXCHANGE WEB SERVICES PROTECTION FOR SKYPE-FOR-BUSINESS
SphereShield eliminates this risk. It blocks any information requests arriving from unregistered devices and adds a Two Factor Authentication (TFA) layer for the Exchange.
The solution is based on a Two Factor Authentication process, which uses the client’s password and device. The result is that unauthorized usage of the user’s credentials is not sufficient to connect to Skype for Business or Exchange without having access to the device itself. This also enables restricting the usage of these services to approved or registered devices only.
Disable “Save Password” option
Companies that do not want passwords to be cached in the device may disable the “Save Password” option on Skype for Business.
Choosing this option, however, creates difficulties in accessing the Exchange during the ongoing usage of Skype for Business as the Exchange requires credentials that were not saved on the device and therefore no longer exist. This causes the user to receive an error.
SphereShield offers a solution for this scenario, enabling a smooth user experience for continuous connectivity to Skype for Business and Exchange without saving the password on the device.
This allows the user to deploy the disabled “Save Password” option and still stay connected to the Exchange until the user signs out, thus not compromising on security as well as user experience.
SphereShield offers several approaches for registering and approving mobile devices using the Skype for Business access control module. The registration process is done by using SphereShield Access Portal, a self-service Web portal.
Device Registration Options
Skype for Business Access Control supports the following enrollment options:
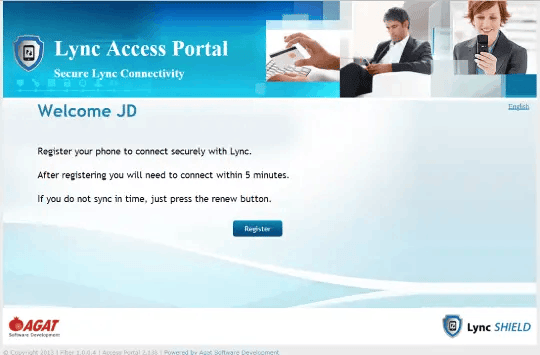
· Two step registration – a tighter security approach which requires users to register first on a dedicated access portal and connect within a short period (defined in the portal configuration). In such a scenario, the user logs into the access portal with his active directory credentials (window authentication) from an internal network PC. After doing so, he is asked to press the register button and to perform a Skype for Business connectivity operation within a limited period defined by the admin (default is 15 minutes). Once the user successfully connects his device, it is registered. From that point on, SphereShield will only allow the current user to connect from the registered device.
· A user can add another device if SphereShield is configured to support multiple devices. SphereShield can also limit the number of devices approved for a user to a specific number.
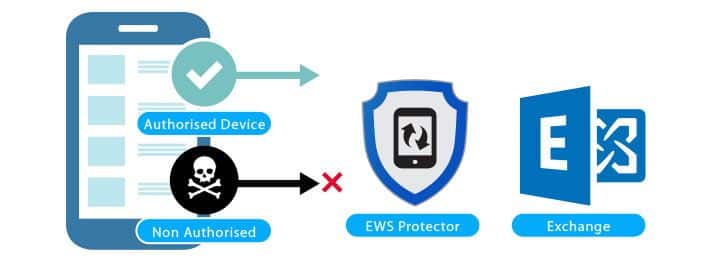
· Matching the device and user
· Two step strong verification
· Avoid connection to Skype for Business servers by hackers and other unauthorized users