DATA LOSS PREVENTION (DLP) FOR SKYPE-FOR-BUSINESS
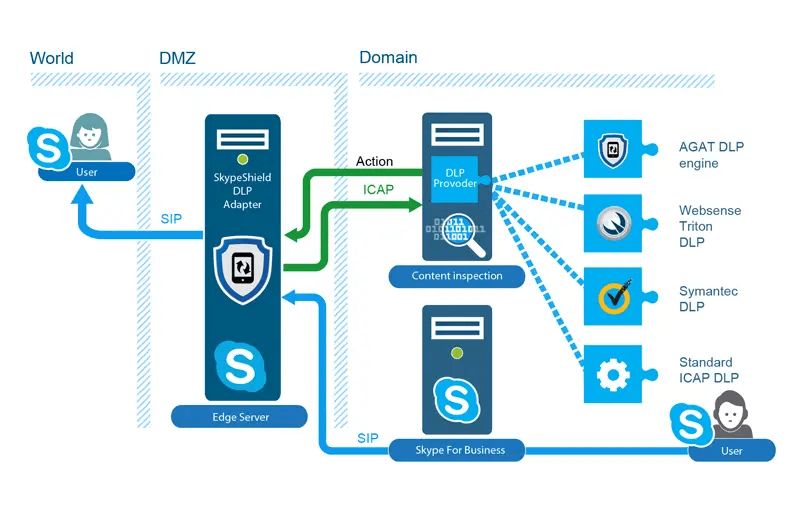
As the usage of Skype for Business extends outside the network boundaries, enabling communication with external parties via federation meetings poses some serious security and data protection risks. This arises from the fact that data flow between parties is very accessible and easy to use at any time, in any place, and by any device.
Preventing data leaks from going through Skype for Business is a challenging undertaking because of the variety of mobile, web and desktop clients that Skype for Business services, and because of the SIP protocol in use by the clients.
Skype for Business offers a new approach for content and data transfer inspection outside the regular inspection areas of most vendors. The concept is based on a server side inspection and therefore covers all of the channels possible by Skype for Business infrastructure regardless of the client in use.
The solution is based on a content inspection module with an adapter that is able to send the content via ICAP protocol to a DLP provider. The adapter can be configured to work with DLP commercial vendors, such as Symantec DLP or ForcePoint (Websense), or any standard DLP vendor that supports ICAP.
In addition, SphereShield offers a built-in DLP engine for customers that do not have an existing DLP commercial solution in place.
The DLP module modifies the messages according to incident response from the DLP provider. This includes blocking the content, masking sensitive parts, sending an IM message warning notification to the sender, or just monitoring and alerting.
SphereShield built-in DLP engine
For companies that do not have an existing DLP product, SphereShield offers a built-in DLP engine.
The DLP engine inspects the content going through Skype for Business IM and binary files, preventing content from exiting the network based on a set of out-of-the-box and configurable rules detecting content such as credit card numbers, social security numbers, and others.
Content is scanned “on the fly” and action is taken – depending on the policy defined – blocking the full content, masking the forbidden text or notifying the DLP team.
For companies looking to prevent harassment issues among employees, SphereShield uses the DLP Rules in the AGAT DLP infrastructure which implements two separate rules that together create the Anti-harassment and Workplace Safety Policy compliance. The first rule is “Badwords” which contains a list of profanities that would be used in a bullying or sexual harassment scenario. The second rule is “inappropriate emojis” which contains a list of emoticons that could be used in a bullying or sexual harassment scenario such as, kiss, swear, in-love, heart, broken heart, hug, wink, grin, devil, head-bang, and punch.
Commercial DLP adapter
Highlights
· Inspect traffic from any Skype for Business client type (PC, Mobile, Web)
· Built-in DLP engine with configurable policy rules
· Support block, mask or notify of DLP incident
· IM sent to user when incident detected
· Integration with commercial DLP vendors via ICAP like Websense & Symantec
· Using the DLP Rules in the AGAT DLP infrastructure, SkypeShield implements two separate rules that together create the Anti-harassment and Workplace Safety Policy compliance.