In this second delivery, we continue to reveal the top 10 security Threats to Microsoft Teams
If you haven’t read the first part here’s the link: https://agatsoftware.com/blog/ten-security-threats-to-microsoft-teams-part-1/
Fourth Threat: Malware Uploaded through Microsoft Teams Files
External users could upload malware from unmanaged devices.
Guest devices aren’t company managed, so their particular status remains unknown. That includes the existence of certain anti-malware tech. Microsoft Teams channels may include several internal users, each of which is capable of a security breach via a malicious file upload.
IT admins will need to be able to block every file upload coming from an unmanaged device, or they should be able to scan uploaded content before removing it from a channel. IT management should be informed of these types of incidents.
Soultion: Threat-protection For Microsoft Teams Teams
Fifth Threat: Data Loss through Filesharing and Teams Chats
Filesharing on Microsoft Teams can result in the loss of confidential data.
Microsoft Teams allows users to collaborate on and share files. They also have the option to chat with other members. Each of these features could end up being data loss conduits, and must be regulated.
DLP technology with sensitive content-identifying abilities must be implemented directly on Microsoft Teams file shares and chats. It should include features like exceptional logic, Boolean logic for the sake of checking multiple parameters, proximity checking, file fingerprinting, dictionary matches for specific organizations, and standard DLP data identifiers.
The scans must have the ability to be performed in real-time or as close to it, as far as file uploads and messages are concerned. Further, scanning on-demand should also be an option for the sake of looking at previously shared files and messages sent within the group. Be mindful that outside users are also capable of uploading sensitive data.
Solution: Real Time DLP For Microsoft Teams
Sixth Threat: Data Loss by Way of Other Apps
Microsoft Teams application integration can result in data being sent to an unknown destination.
Microsoft Teams lets users incorporate several independent apps that are cloud-based directly into their group environments. It provides features like sales apps, project management, HR, education, business intelligence, analytics, and polling. As beneficial as these apps are to users, independent applications come with data loss risks and security concerns. Data may get passed to another service provider outside the Microsoft Teams system.
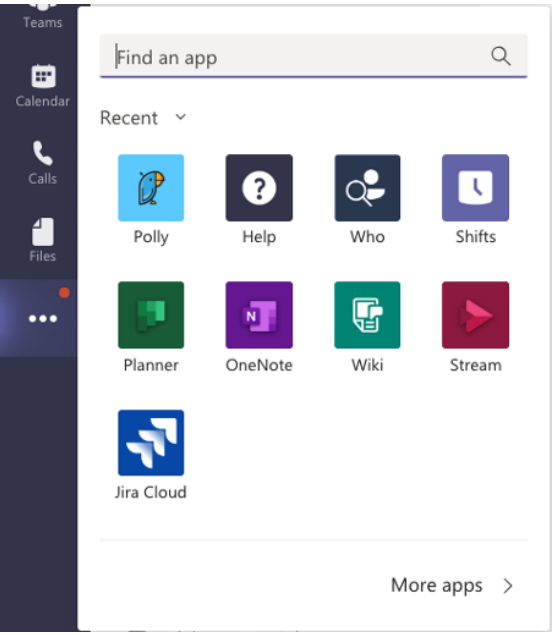
Many apps are capable of transferring data through their own services. As such, IT administrators will require a system that can discover independent apps that are in use. Their risk profiles must be reviewed, and a workflow will need to be provided to notify, block, allow, audit, or remedy ate users of the app’s status. Access can be revoked as needed.
Seventh Threat: Sluggish Security is a Lot Better than Zero Security
Certain actions must be performed in real-time, lest you risk the data from being lost. Your security system may not be quick to respond, but that is a lot better than not having any security, which will only result in complacency.
Enforcement systems must support numerous actions based on the violation severity. Multiple actions must be available, including the following:
- Adding incidents to the incident log.
- Deleting a chat or file from the Microsoft Teams channel.
- Removing the file’s shared link.
- Quarantining a file, letting IT admins release it once it’s safe.
- Quarantining a file, letting users release it once it’s safe.
- Removing a user from the channel.
- Either applying classification or DRM tags, or encrypting the file.
- Sending notifications to bots, administrators, users, and other relevant people.
Microsoft Teams comes with several APIs (application programming interfaces) which may be used for security implementation. With that said, not all vendors prioritize this. As such, incident response times can be quantified in either minutes or even hours – meanwhile, incidents involving data loss might have already occurred. IT admins must check general response times regarding incident remediation. They need to make sure that responses are as close to real-time as possible.
Stay tuned for our third and final delivery.